The power of penetration testing to identify security risks
In an era dominated by technology, ensuring the security of digital assets has become paramount. Penetration testing, often referred to as pen testing, stands as a crucial practice in identifying and addressing security risks. As organizations increasingly rely on digital infrastructure, the need to safeguard sensitive information from cyber threats has never been more critical.
Importance of Security
As the digital landscape expands, so do the threats that loom over organizations and individuals alike. Cybersecurity breaches have become increasingly sophisticated, making it imperative for entities to fortify their defenses. The consequences of a security breach extend beyond financial losses; they include reputational damage and the compromise of sensitive data. Thus, the importance of robust security measures cannot be overstated. Do you know the most reliable machine MAC by Apple is also vulnerable to cyberattacks? If don’t then find about it by clicking here.
Understanding the Essence of Penetration Testing
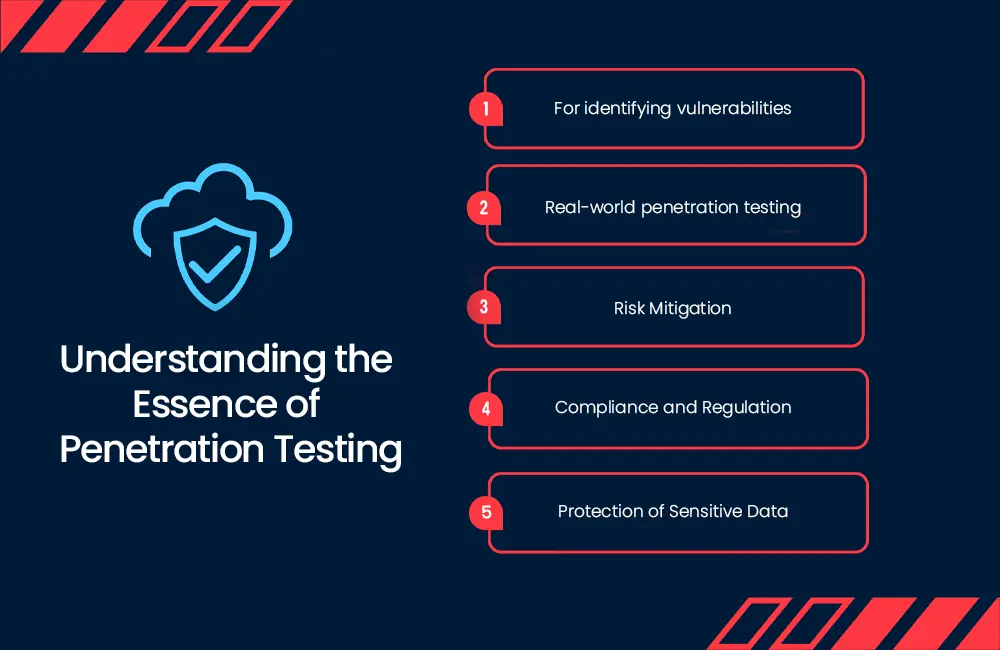
At its core, penetration testing, often colloquially referred to as pen testing, is a simulated cyberattack on systems, networks, or applications. This ethical hacking approach aims to identify and uncover vulnerabilities before they can be exploited by malicious actors. In a world where digital threats are pervasive, pen testing becomes a critical element in fortifying digital infrastructures.
- For identifying vulnerabilities
There’s a variety of vulnerabilities out there. Some are familiar, known vulnerabilities, while others are zero-day vulnerabilities, freshly uncovered but not yet patched. Penetration testing plays a crucial role in unveiling the flaws within a system that might not be evident through routine security assessments.
- Real-world penetration testing
Engaging in penetration testing can add an element of excitement to identifying vulnerabilities. These tests simulate real-world cyber attacks, offering companies a practical evaluation of their security stance. And you know what? It gives them insights into how well their defenses would hold up against genuine threats.
- Risk Mitigation
Identifying weaknesses before attackers exploit them offers a significant advantage—mitigating substantial risks when organizations stay a step ahead of potential threats. Taking proactive measures, such as reconfiguring systems, patching software, or implementing additional security protocols, falls under this proactive risk mitigation approach.
- Compliance and Regulation
In certain industries and regions, pen testing is subject to strict regulation and compliance standards. Meeting these requirements is crucial to circumvent legal and financial repercussions, highlighting the pivotal role of adherence in specific sectors.
- Protection of Sensitive Data
Penetration testing assumes a pivotal role in safeguarding sensitive data, financial records, and confidential information. Its primary objective is to ensure that data remains adequately shielded from unauthorized access or theft, emphasizing the critical role of pen testing in data protection.
Benefits of Penetration Testing

Penetration testing offers a proactive approach to security by simulating real-world attacks. By doing so, organizations can pinpoint vulnerabilities before malicious actors exploit them. This not only minimizes the risk of data breaches but also allows for the implementation of targeted security measures. Furthermore, penetration testing provides insights into potential weaknesses in processes and personnel, allowing for comprehensive risk mitigation. Find about vulnerabilities found in 2023 by clicking here.
Types of Penetration Testing
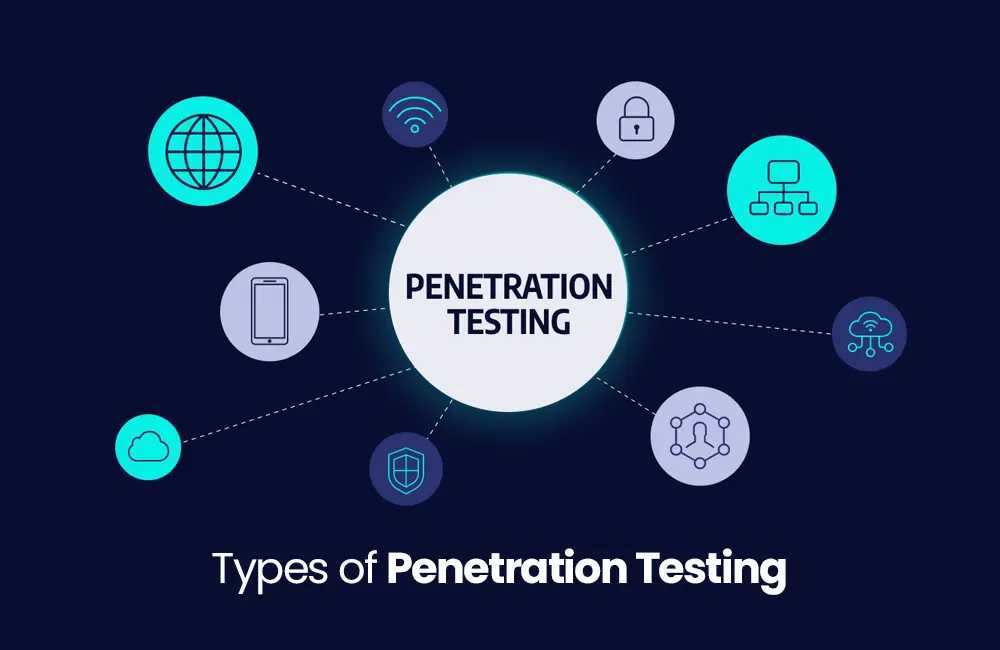
One of the primary classifications is network penetration testing, focusing on evaluating the security of networks and systems. This method helps assess the robustness of an organization’s infrastructure against potential threats. Other types include web application testing including Injection Attacks, Broken Authentication, Sensitive Data Exposure, mobile application testing, and social engineering assessments. Each type addresses specific aspects of an organization’s digital presence, ensuring a comprehensive evaluation of potential vulnerabilities.
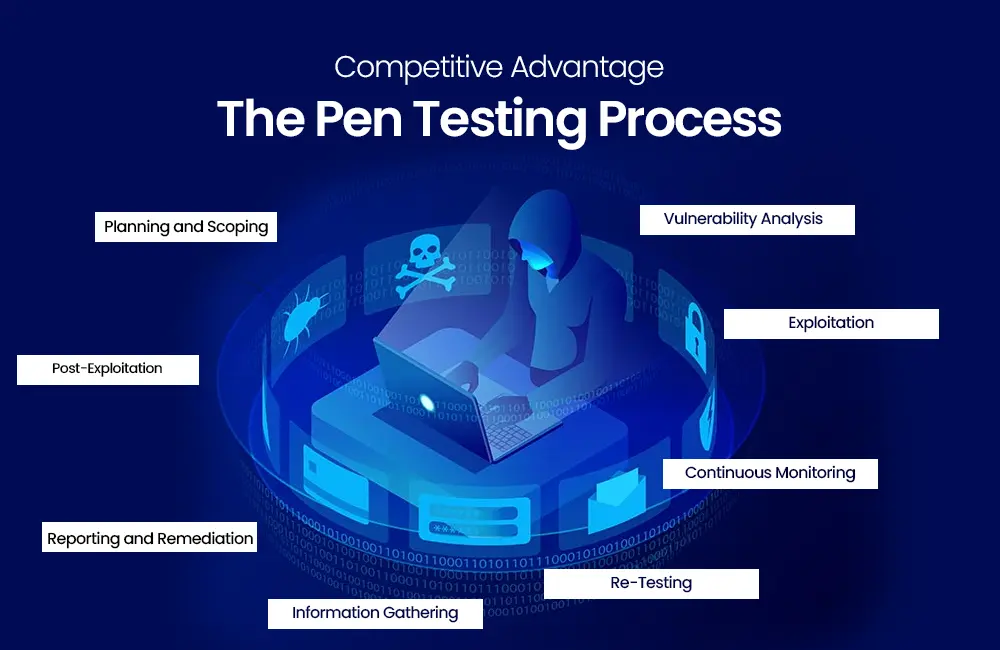
The Process of Penetration Testing
Successful penetration testing begins with meticulous planning and scoping. Understanding the objectives and potential risks sets the stage for a comprehensive evaluation. The testing process involves the identification of targets, vulnerability analysis, and exploitation attempts. Throughout this process, ethical hackers, often referred to as “white hat” hackers, mimic the actions of malicious actors to uncover potential security weaknesses.
Tools Used in Penetration Testing
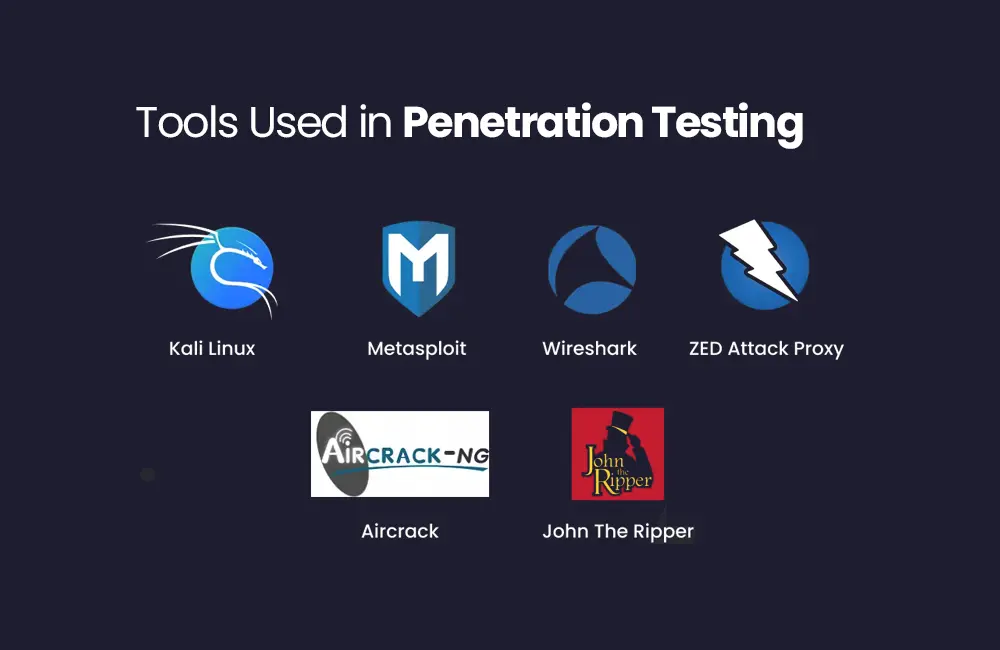
The arsenal of tools available for penetration testing is vast. From widely used tools like Metasploit to specialized options like Wireshark, each plays a crucial role in uncovering vulnerabilities. Automated scanners, such as Nessus and OpenVAS, streamline the process of identifying common vulnerabilities. However, the effective use of these tools requires expertise and a deep understanding of the organization’s specific infrastructure.
Real-world Examples
High-profile breaches underscore the critical need for penetration testing. Case studies of organizations that fell victim to cyberattacks highlight the real-world consequences of inadequate security measures. The Equifax breach in 2017, where sensitive personal information of millions was compromised, serves as a stark reminder of the far-reaching impact of security lapses.
Challenges in Penetration Testing

The dynamic nature of cyber threats poses challenges to penetration testing. Adapting to an ever-evolving threat landscape remains a constant struggle for security professionals. New attack vectors emerge, and threat actors continuously refine their tactics. Overcoming these challenges requires a proactive mindset, continuous education, and a commitment to staying ahead of emerging threats.
Industry Compliance and Penetration Testing
Regulatory bodies increasingly mandate penetration testing as part of compliance requirements. Meeting these standards not only ensures legal adherence but also enhances overall security posture. Industries such as finance and healthcare, handling sensitive customer data, are particularly subject to stringent regulations. Compliance with standards like PCI DSS and HIPAA is not only a legal requirement but also a fundamental step in building trust with customers.
Future Trends in Penetration Testing

The integration of artificial intelligence in penetration testing is a promising avenue. Automated tools can enhance the efficiency and accuracy of identifying vulnerabilities. Machine learning algorithms can analyze vast datasets to identify patterns and anomalies that may elude human analysts. However, the human element remains crucial for interpreting results, understanding context, and making informed decisions based on the findings.
Tips for Effective Penetration Testing
Collaboration and communication are key components of successful penetration testing. Engaging stakeholders and fostering a culture of security awareness contribute to a robust defense strategy. Regular communication between security teams, IT personnel, and management ensures that everyone is aligned in understanding potential risks and implementing necessary security measures.
Hiring Professional Penetration Testers
The demand for skilled professionals in penetration testing is rising. Certifications like Certified Ethical Hacker (CEH) and Offensive Security Certified Professional (OSCP) validate the expertise of pen testers. Organizations should prioritize hiring individuals with a comprehensive understanding of different testing methodologies, ethical standards, and a commitment to ongoing professional development. To get services for professional penetration testers follow us on LinkedIn.
Case Studies
Examining successful security implementations through case studies provides practical insights. Understanding how other organizations secured their systems informs effective security strategies. The implementation of multi-factor authentication, regular security audits, and employee training programs are common threads in successful case studies. Learning from these examples helps organizations tailor their security measures to their specific needs and challenges.
Common Misconceptions
Distinguishing penetration testing from ethical hacking is essential. While both share common goals, they differ in approaches and methodologies, each serving a unique purpose in the cybersecurity landscape. Ethical hacking encompasses a broader scope, including vulnerability analysis, risk assessment, and proactive security measures. Pen testing, on the other hand, specifically focuses on identifying and exploiting vulnerabilities to assess the effectiveness of existing security measures.
Common Web Application Security Risks Demystified

Ever wondered about the typical security risks web applications face? Let’s break it down:
- Injection Attacks
Sometimes, untrustworthy data sneaks into the interpreter as part of a command. This can lead to unintended commands executing or unauthorized access to data. It’s like a security sneak attack, and we call it an injection attack. Think SQL injection, NoSQL injection, and OS command injection as the troublemakers here.
- Broken Authentication
Imagine a weak link in the authentication system—attackers could exploit it to snag sensitive info. Weak passwords, vulnerabilities in session management, shaky password resets, and credential recovery mishaps are the culprits behind broken authentication.
- Sensitive Data Exposure
Picture this: not safeguarding sensitive data properly could open the floodgates for unauthorized access and potential theft. Whether it’s insecure storage, mishandling data, or lacking encryption, it’s a risk you definitely want to avoid.
Conclusion
In conclusion, the power of penetration testing lies in its proactive approach to security. As threats evolve, so must our strategies. Vigilance, collaboration, and staying ahead of emerging trends will determine the success of cybersecurity measures. Organizations that prioritize penetration testing as an integral part of their security strategy are better equipped to identify and address vulnerabilities before they can be exploited.